Onshore vs Offshore for Microsoft Power Platform in Regulated Industries
Many Microsoft teams adopt offshore delivery models for cost reasons. On paper, the savings can look compelling. In regulated environments, however, the real cost rarely shows up in the hourly rate. Most Power Platform programs break later in the lifecycle. Teams ship flows, apps, and integrations quickly, but ownership, testing evidence, and release controls lag. When your organization relies on distributed or loosely governed Power Platform development services, these gaps often appear months later as incidents, rework, or audit friction.
That is why many enterprise leaders reconsider how they structure Power Platform consulting services for compliance-heavy Microsoft 365 environments. The decision is less about labor location and more about operational control. When automation, approvals, and data access run through a regulated Microsoft environment, delivery models must support traceable changes, enforceable governance, and production accountability from the start.
Choose a Safer Model for Power Platform Delivery
i3solutions delivers governance-first Power Platform development services and Power Platform consulting services for compliance-heavy Microsoft 365 environments, helping your enterprise release automation with clear ownership and audit-ready change control.
Quick Summary:
In regulated Microsoft 365 environments, Power Platform delivery is not a commodity. Offshore teams may reduce upfront costs, but often create hidden operational, compliance, and audit risks. Onshore delivery ensures traceable ownership, enforceable governance, faster incident response, and audit-ready evidence. Hybrid models can work only for low-risk, non-production tasks under strict oversight.
Key Takeaways:
- Offshore delivery may lower hourly rates but increases governance overhead, rework, and compliance risk.
- Power Platform acts as a control surface for sensitive business processes, requiring traceable change management.
- Onshore teams improve operational accountability, decision speed, and audit defensibility.
- Data sensitivity, DLP policies, and tenant-level exposure make location and governance critical.
- Hybrid delivery is viable only for low-risk tasks with strong templates and onshore oversight.
- Total cost of risk often exceeds apparent labor savings, making governance-first delivery the safer choice.
Why Power Platform in Regulated Industries Is Not a Commodity Build
In regulated Microsoft environments, Power Platform is not simply a low-code productivity tool. It becomes part of the operational control layer for business processes, approvals, and data movement. That means design decisions affect security posture, audit evidence, and production stability across the Microsoft 365 environment.
Many organizations initially treat Power Platform development like commodity application work. Teams build apps, flows, and integrations quickly, often through distributed or offshore delivery models. The problems usually appear later when changes accumulate, ownership becomes unclear, and incident response depends on tribal knowledge rather than enforceable runbooks.
This is where the delivery structure starts to matter. Leaders evaluating offshore models often focus on hourly cost. The more important question is how the model supports governance, change control, and operational accountability across a regulated Microsoft environment.
Power Platform as a Control Surface, Not Just an App Builder
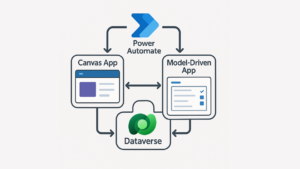
In enterprise Microsoft environments, Power Platform acts as a control surface for business operations. Power Apps can manage regulated workflows, while Power Automate often orchestrates approvals, data transfers, and system integrations.
When those automations touch sensitive processes, every release becomes a controlled change. Leaders must know what was modified, who approved it, and what testing evidence supports the release. Without those controls, automation increases operational risk rather than reducing it.
This is one reason many CIOs revisit delivery models after early incidents. The real issue is not where developers sit. The issue is whether the delivery structure supports production ownership and enforceable change validation.
Data Sensitivity, Identity, and Tenant-Level Risk in Microsoft 365 and Power Platform
Power Platform operates directly inside the Microsoft 365 environment. Flows connect to SharePoint, Dataverse, Dynamics 365, and external APIs, often using privileged service accounts or delegated identity permissions.
That creates tenant-level exposure if governance controls are weak. A single automation change can affect sensitive data flows, financial approvals, or compliance reporting. When incidents occur, organizations must show who approved the change and how it was validated.
This reality is often what drives internal conversations about how to justify onshore Power Automate services to finance and procurement. The argument is not about geography. It is about operational accountability. In regulated environments, leaders must ensure that the teams building automation can support controlled releases, defend design decisions, and produce audit-ready evidence when regulators or internal risk teams ask for proof.
The Traditional Offshore Promise vs. the Reality in Regulated Environments
Offshore delivery models are often positioned as the logical choice for enterprise software programs. In discussions around Onshore vs. Offshore Power Platform Development, the message is usually straightforward: lower hourly rates, large teams, and the ability to scale quickly. For commodity development tasks, that model can work.
Power Platform programs in regulated Microsoft environments operate under different constraints. Automations control approvals, financial processes, and regulated data flows. When those systems fail or release incorrectly, the downstream impact is operational, not just technical.
This is typically the moment CIOs and enterprise architecture leaders reassess the Power Platform delivery model. The real cost is rarely the initial build. It appears later through governance overhead, release friction, and repeated rework.
How Offshore Models Are Sold to CIOs and CFOs
Offshore delivery models are typically presented using a predictable value narrative. The focus is on immediate cost reduction and delivery capacity rather than long-term operational accountability.
Common selling points include:
- Lower hourly rates: Labor arbitrage is positioned as the primary financial advantage. Rate comparisons dominate procurement discussions.
- Large delivery teams: Offshore providers emphasize the ability to scale quickly using large development pools.
- Factory-style delivery: Work is structured into tickets and throughput metrics rather than production ownership.
- Follow-the-sun development: Continuous development cycles are marketed as a productivity advantage.
- Standardized implementation models: Providers promote repeatable build frameworks that appear efficient on paper.
These arguments resonate with procurement and finance teams reviewing budget line items. However, they rarely account for how automation actually behaves inside a regulated Microsoft environment. CIOs responsible for production stability eventually discover that automation delivery cannot be managed like a commodity factory.
The Hidden Costs: Governance Overhead, Time Zone Friction, and Rework
The operational reality usually appears several quarters into the program. Initial builds ship quickly, but governance gaps and release friction begin to surface.
Common patterns we see in large enterprises include:
- Governance overhead increases: Internal architecture and risk teams must review and validate every change because ownership is fragmented.
- Time zone coordination slows releases: Approvals, testing, and troubleshooting stretch across multiple working days.
- Knowledge fragmentation: Context about flows, connectors, and data contracts spreads across distributed teams.
- Incident recovery becomes slower: Operations teams struggle to trace what changed and who implemented it.
- Rework becomes routine: Automation must be redesigned to meet compliance or security requirements after deployment.
This is where your leaders should start analyzing the cost of rework with offshore Power Automate developers in large enterprises. The direct cost of rebuilding flows, correcting identity permissions, or redesigning approval logic often outweighs the original development savings.
In sectors with sensitive intellectual property or export-controlled systems, the delivery model becomes even more critical. Many organizations eventually move toward an onshore Power Platform implementation partner for aerospace and defense manufacturers or similarly regulated industries. The shift reflects a simple operational reality: when automation touches regulated processes, production accountability matters more than initial labor cost.
Risk Profile of Offshore Power Platform Delivery in Compliance-Heavy Organizations
Automation is not just a development task. Power Platform changes can affect approvals, financial workflows, operational reporting, and sensitive data flows. When delivery teams lack deep process understanding, automation amplifies existing problems rather than solving them. This often leads to higher costs and lengthy recovery periods rather than the promised gains. That means delivery decisions directly influence compliance posture and incident risk.
Many enterprises discover this after initial deployments. Automation grows quickly, but governance maturity lags. This is where Power Platform governance risks with offshore development teams often become visible to security, compliance, and operations leaders.
The issue is rarely developer capability. The risk emerges when delivery structures make it difficult to enforce controls, validate changes, and prove accountability across a regulated Microsoft environment.
Data Handling, Jurisdiction, and Regulatory Exposure
When Power Platform solutions process regulated or sensitive information, data handling becomes a governance issue rather than a development detail.
Common risk patterns include:
- Cross-border data exposure: Developers working outside regulatory jurisdictions may interact with systems containing controlled or sensitive data.
- Privileged access expansion: Service accounts, connectors, and delegated permissions increase the blast radius of configuration mistakes.
- Unclear accountability chains: When delivery teams are distributed globally, ownership of automation logic and data handling becomes difficult to trace.
- Access review complexity: Security teams struggle to validate who can modify flows or applications affecting regulated processes.
- Delayed remediation: If risky automation patterns are discovered, coordinating changes across distributed teams slows response.
For organizations with strict compliance obligations, these concerns move the delivery discussion beyond cost. Your business leaders must guarantee that the people building automation operate inside governance models that match the organization’s regulatory exposure.
DLP Policies, Connectors, and Shadow Integrations
Power Platform integrates deeply with services across the Microsoft environment and external systems. Without strong enterprise governance, automation can quietly bypass established architectural controls.
Common breakdowns include:
- Connector misuse: Teams introduce connectors that bypass approved integration pathways or data classification rules.
- Weak Data Loss Prevention enforcement: DLP policies exist, but developers create exceptions to meet delivery deadlines.
- Shadow integrations: Power Automate flows connect systems outside approved API layers or integration governance.
- Environment sprawl: Development environments multiply, making it difficult to enforce consistent policy and monitoring.
- Inconsistent design patterns: Flows and apps are built differently across teams, increasing operational complexity.
These patterns usually emerge gradually. Over time, the Microsoft environment accumulates invisible dependencies and undocumented data paths that are difficult to control.
Audit, Incident Response, and Proving Control to Regulators
The final risk appears when something goes wrong. In regulated organizations, incidents must be investigated with clear operational evidence.
Operational challenges often include:
- Missing release evidence: Teams cannot quickly show who approved or tested a change before it went live.
- Limited traceability: When incidents occur, operations teams struggle to determine which automation introduced the problem.
- Slow incident recovery: Troubleshooting requires coordination across multiple distributed teams with fragmented context.
- Audit preparation becomes reactive: Compliance teams spend weeks collecting artifacts that should already exist.
- Defensibility gaps: Leadership cannot easily prove that automation changes follow a repeatable governance process.
For CIOs and risk leaders, this is the defining question: Can the organization demonstrate control over automation running inside its Microsoft environment? When delivery models weaken that control, operational risk increases regardless of the original development cost.
Onshore Delivery Models: Where the Real Advantage Shows Up
Proximity to Risk Owners: CIO, CISO, Compliance, and Internal Audit
The advantage of onshore Power Platform delivery is rarely about lower hourly rates. It shows up in operational control, decision defensibility, and the ability to respond quickly when governance, compliance, or production issues arise. In regulated environments, teams must be close to risk owners (CIOs, CISOs, compliance, and internal audit). When questions surface about approvals, data handling, or incident evidence, onshore teams can provide immediate clarification and actionable context.
Understanding Healthcare, Financial Services, and A&D Requirements
Onshore partners bring visibility into industry-specific regulations that offshore teams often miss. Healthcare, financial services, and aerospace and defense organizations face obligations beyond generic Microsoft 365 governance. Local delivery teams align Power Apps, Power Automate flows, and Dataverse configurations to meet audit expectations while minimizing downstream rework. They understand exactly what proof auditors will require and embed controls into automation from the start.
Faster, Defensible Decisions for Risk and Oversight Committees
Decision-making accelerates when teams are geographically aligned. Risk and oversight committees can review approvals, validate changes, and address exceptions without waiting for time-zone handoffs. For enterprise leaders asking who should build Power Automate workflows in a regulated enterprise: onshore vs. offshore partner?, the operational reality favors onshore. This model reduces rework, strengthens compliance, and delivers traceable governance across Microsoft environments. These benefits far outweigh any initial cost savings from offshore delivery.
Total Cost of Risk vs. Hourly Rate: A Structured Comparison
Choosing offshore or onshore Power Platform delivery is rarely about the hourly rate. Early decisions on team location, change governance, and validation affect compliance, production stability, and audit defensibility. The total cost of risk unfolds over months or years, often exceeding initial labor savings.
Direct Costs
Offshore delivery can create hidden operational costs. Flows and apps often require rework to meet compliance standards. Go-lives get delayed because approvals and testing span multiple time zones. Failed audits trigger emergency remediation and extended review cycles. Even small mistakes in Power Automate logic or connector configuration can ripple across departments. When automation touches sensitive or regulated data, every correction disrupts workflows and reporting.
Indirect Costs
Indirect costs are harder to quantify but equally impactful. Repeated “do-over” initiatives erode team confidence in automation. Leadership hesitates to approve new flows, slowing innovation. Internal audit teams spend excessive time validating evidence that should exist automatically. Over time, these costs reduce agility and increase the perceived risk of every new initiative.
Example Scenario
A distributed offshore team builds a financial approval flow. A connector bypasses DLP policies, exposing sensitive data. The audit flags the issue. Teams must redesign the flow, validate changes, and produce evidence. Leadership confidence drops, reporting is delayed, and the cost multiplies.
For enterprise leaders weighing delivery models, the lesson is clear. When you compare offshore vs. US-based Power Platform development companies, upfront labor savings rarely outweigh the direct and indirect costs of risk. Onshore delivery ensures faster remediation, stronger compliance alignment, and traceable governance across Microsoft environments.
Comparison Table: Offshore vs. Onshore Power Platform Delivery in Regulated Industries
| Decision Factor | Offshore Power Platform Delivery | Onshore Power Platform Delivery |
| Upfront Cost | Lower hourly rates and larger staffing pools. | Higher hourly rates but smaller senior-led teams. |
| Governance Enforcement | Often fragmented across distributed teams and handoffs. | Governance is embedded directly into delivery workflows. |
| Production Ownership | Ownership is frequently unclear after deployment. | Clear accountability for flows, apps, and connectors. |
| Audit Readiness | Evidence collection is often manual and reactive. | Release approvals and testing evidence are documented from the start. |
| Incident Response | Troubleshooting slowed by time-zone gaps and fragmented context. | Faster investigation with direct access to decision-makers and architects. |
| Data & Compliance Risk | Greater exposure when teams access regulated systems across jurisdictions. | Stronger control over identity, data access, and change management. |
| Rework Likelihood | Higher risk of redesign when compliance or DLP issues appear later. | Lower rework due to governance-first design and approval gates. |
| Long-Term Cost | Hidden costs emerge through rework, audit remediation, and delays. | Higher upfront cost but lower operational risk and lifecycle cost. |
Reduce the Hidden Costs of Power Platform Delivery
Onshore delivery minimizes rework, audit friction, and operational risk across regulated Microsoft environments. We help enterprises compare offshore vs. US-based Power Platform development companies and choose a governance-first approach.
When Offshore or Hybrid Can Work – and Under Strict Guardrails
Offshore or hybrid delivery can succeed in regulated Microsoft environments but only under tightly enforced controls. Without clear boundaries, distributed teams introduce compliance, audit, and operational risk. Successful models combine onshore oversight with offshore execution, applied selectively to low-risk tasks.
Low-Risk Use Cases and Non-Production Environments
Offshore teams are best suited for scenarios that do not impact production or regulated data directly:
- Development in sandbox or test environments.
- Building templates or reusable components that require minimal compliance review.
- Automation for non-critical workflows with low data sensitivity.
- Prototype apps or proofs-of-concept where errors have no operational or regulatory impact.
Onshore Governance, Offshore Execution Under Strict Templates
When using hybrid models, governance remains the onshore team’s responsibility. Offshore execution should follow strict templates and pre-approved processes:
- All flows and apps must adhere to predefined design patterns and DLP policies.
- Onshore teams review and approve all changes before production deployment.
- Time-zone coordination and documentation are standardized to avoid gaps in ownership.
- Operational runbooks and evidence logs are maintained by the onshore governance team.
Minimum Governance Artifacts Before Offshoring Any Power Platform Work
Before distributing Microsoft Power Platform development offshore, enterprises must enforce baseline controls:
- Environment inventory and access matrix documented and approved.
- Data handling policies and DLP enforcement are in place.
- Release gates and testing validation procedures are clearly defined.
- Audit-ready approval evidence for flows, apps, and connectors.
- Defined escalation paths for incidents or deviations from templates.
Leaders evaluating onshore vs. offshore Power Platform development for regulated industries should treat offshore execution as a controlled extension, not a replacement, of governance. When guardrails are in place, hybrid delivery can provide scale without compromising compliance or operational stability.
A Practical Decision Checklist for IT Decision Makers
Selecting the right delivery model for Power Platform initiatives in regulated Microsoft environments requires more than a cost comparison. Leadership must weigh operational risk, compliance obligations, and governance accountability. A structured decision checklist helps ensure all critical factors are addressed before committing to offshore or hybrid models.
Questions to Ask About Any Offshore Power Platform Proposal
When evaluating proposals, IT leaders should focus on operational control and enforceable evidence, not just cost or speed:
- Who owns production accountability for flows, apps, and connectors?
- How will DLP policies, sensitive data handling, and environment controls be enforced?
- What evidence will be produced for every release to satisfy audit requirements?
- How are time-zone gaps, approvals, and emergency incidents managed?
- What mechanisms exist to prevent shadow integrations or uncontrolled changes?
- Is offshore Power Automate development safe for healthcare and financial services?
If answers are vague or rely solely on “standard processes,” the model introduces measurable compliance and operational risk.
What You Must Be Able to Explain to Risk, Audit, and the Board
Before approving any offshore delivery, CIOs and risk leaders must be ready to show:
- Clear ownership and accountability for every automation deployed.
- Traceable approval evidence for each flow and app impacting regulated processes.
- Enforceable change gates, test results, and remediation plans.
- How incidents will be investigated, resolved, and documented.
- Alignment with compliance expectations for sensitive data, identity, and tenant-level control.
A structured, evidence-based approach gives leadership confidence that automation will run safely, produce audit-ready evidence, and minimize rework – regardless of where the developers sit. This checklist reframes the discussion from hourly cost to operational and compliance defensibility.
How i3solutions Engages: Governance-First, Onshore-Led Power Platform Delivery
US-Based Senior Microsoft Specialists for High-Risk Workloads
Every i3solutions engagement is delivered by senior, US-based Microsoft specialists. Our teams understand the operational and regulatory realities of healthcare, financial services, and aerospace and defense environments. They manage approvals, flows, and connectors with full traceability, ensuring every change has accountable ownership. Keeping work onshore lets us minimize time-zone delays, improve oversight, and produce audit-ready evidence for internal and regulatory review. This approach establishes confidence that automation will run safely and meet compliance obligations.
Engagement Models: Roadmaps, CoE Setup, Governance, and Delivery
i3solutions offers structured engagement models that combine strategy and delivery:
- Roadmaps: Define automation priorities, compliance requirements, and risk mitigation plans.
- CoE Setup: Establish a governance hub for standards, templates, and reusable components.
- Governance: Implement enforceable controls, approvals, and DLP compliance across Microsoft 365 and Power Platform.
- Delivery: Build and release Power Apps, Power Automate flows, and Dataverse solutions under onshore supervision.
For regulated organizations evaluating the best US-based Power Platform consulting firm, the deciding factors are governance maturity, production accountability, and audit defensibility – not hourly rate. i3solutions delivers onshore-led, governance-first engagements built around those priorities. Every project is structured to be defensible, with senior Microsoft specialists who reduce rework, strengthen compliance, and deliver predictable, enterprise-grade automation across Microsoft environments
Frequently Asked Questions
Even with documented policies, offshore teams add complexity to compliance. Data handling, approvals, and DLP enforcement require local accountability to reduce risk. Without onshore oversight, errors can go unnoticed and expose the organization to audit findings or regulatory violations.
Onshore teams provide immediate access for troubleshooting and approvals. This allows faster remediation of errors or misconfigured flows. Leadership and audit teams can access real-time evidence, reducing downtime and operational disruption.
Hybrid delivery can work if offshore teams are restricted to low-risk or non-production tasks. All high-risk flows and apps must remain onshore under strict governance. Clear templates, approval gates, and runbooks are essential to prevent compliance gaps.
Audit-ready evidence must show who approved changes, how flows were tested, and what controls were applied. This includes DLP logs, connector validations, and release artifacts. Having this information organized before an audit ensures defensibility and reduces manual collection efforts.
Time-zone gaps can delay approvals, troubleshooting, and production fixes. Coordination across distributed teams increases the risk of miscommunication. Onshore governance mitigates these delays by centralizing decision-making and maintaining operational control.
Total cost of risk includes rework, delayed go-lives, failed audits, and lost confidence in automation. These indirect costs often exceed the apparent savings from lower offshore rates. Evaluating risk this way ensures leadership makes decisions based on operational impact, not just hourly cost.
Regulatory nuances in healthcare, financial services, or aerospace and defense are easy to miss without close oversight. Offshore teams rarely have immediate access to decision-makers or compliance experts. Onshore governance ensures automation adheres to DLP, identity, and tenant-level controls consistently.
Offshore work is suitable for low-risk tasks like sandbox development, reusable templates, or prototypes. No production data or sensitive workflows should be involved. Even then, onshore oversight and enforcement of standard templates remain mandatory to reduce operational and compliance risk.
Schedule a Power Platform Governance & Architecture Workshop
Our workshop helps enterprise teams evaluate governance, risk, and architecture decisions around onshore vs. offshore Power Platform development. We assess DLP controls, environment strategy, and release governance across your Microsoft environment. The outcome is a clear, defensible delivery model for secure and compliant automation.
Leave a Comment